Table of Contents
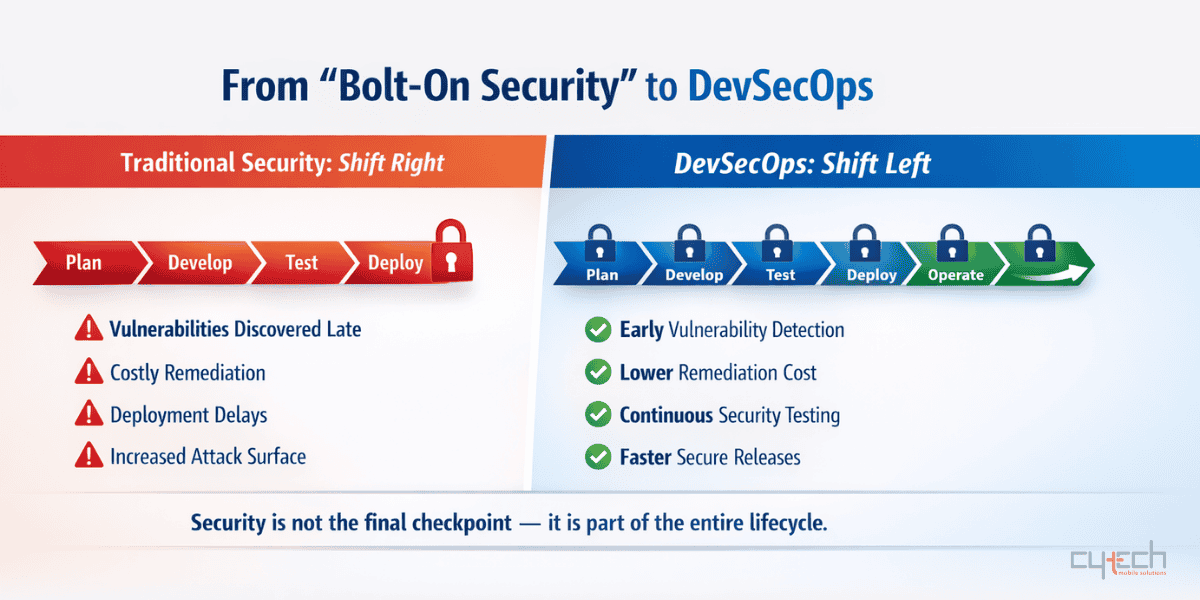
This reactive approach, sometimes called “Shift Right” or “Bolt-On Security,” led to significant challenges. Security vulnerabilities were frequently discovered late in the process, resulting in expensive remediation, deployment delays, and increased risk.
The Problem with “Bolt-On Security”
Imagine building a house and only considering security measures like locks and alarms after the construction is complete. You might find that some doorways are poorly positioned or windows are easily accessible, requiring expensive retrofitting. The same principle applies to software development. When security is addressed late, it becomes:
- Costly: Fixing vulnerabilities in production can cost significantly more than addressing them during the requirements or design phases.
- Inefficient: Rework late in the cycle disrupts development workflows and delays time-to-market.
- Ineffective: Subtle architectural flaws might be impossible to fully remediate without significant restructuring.
- High-Risk: Unresolved vulnerabilities increase the window of opportunity for attackers.
Embracing the “Shift Left” with DevSecOps
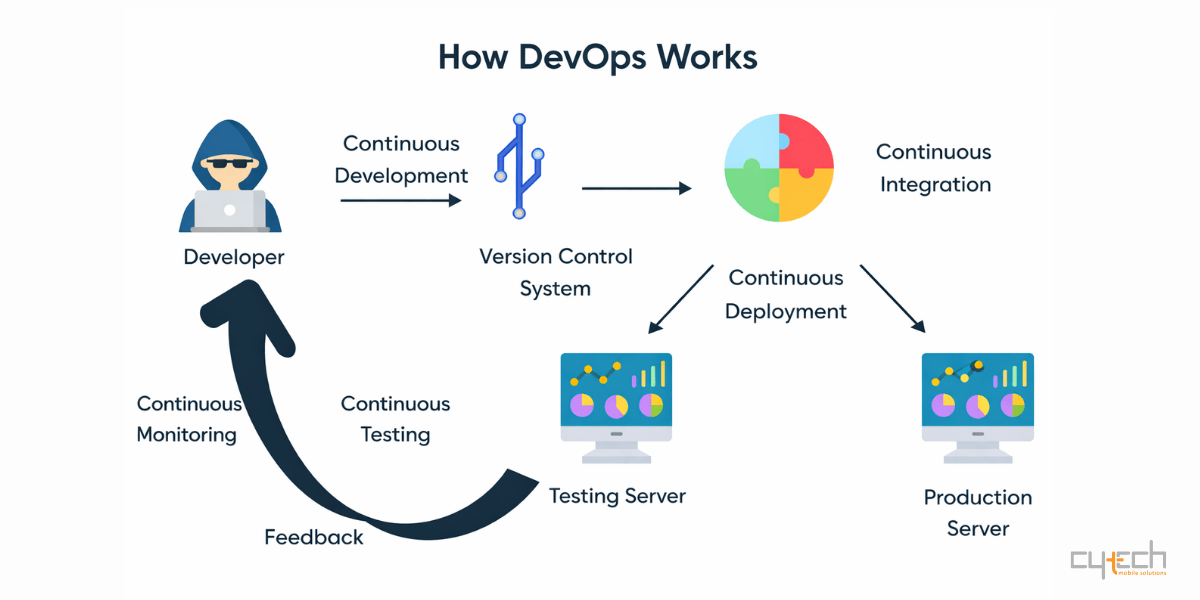
The “Shift Left” in security is a philosophy that advocates for integrating security practices early and throughout the entire SDLC. DevSecOps (Development, Security, Operations) is the cultural and technical manifestation of this principle. It’s about building security into the development process, rather than treating it as a separate, final step.
DevSecOps fosters a collaborative environment where developers, security specialists, and operations engineers work together as a cohesive unit. The primary goal is to make security a shared responsibility, ensuring that secure coding practices, automated testing, and continuous monitoring are inherent to the way software is built.
Comparing Traditional Security vs. DevSecOps
To understand the practical impact of shifting left, it is helpful to look at how security activities change across the lifecycle.
| Feature | Traditional Security (Shift Right) | DevSecOps (Shift Left) |
|---|---|---|
| Timing | Performed at the end of the dev cycle. | Integrated into every phase of the SDLC. |
| Responsibility | Dedicated siloed security team. | Shared responsibility across Dev, Sec, and Ops. |
| Feedback Loop | Slow; weeks or months after code is written. | Fast; immediate feedback via CI/CD pipelines. |
| Testing Style | Manual penetration tests and audits. | Automated scanning (SAST, DAST, SCA). |
| Cost of Fixes | High (Production-level remediation). | Low (Found during coding or build). |
| Deployment Pace | Slowed down by security “gates.” | Accelerated by automated security “guardrails.” |
Key Practices for a DevSecOps Workflow
Adopting DevSecOps requires a combination of cultural changes, process improvements, and the strategic use of automation tools.
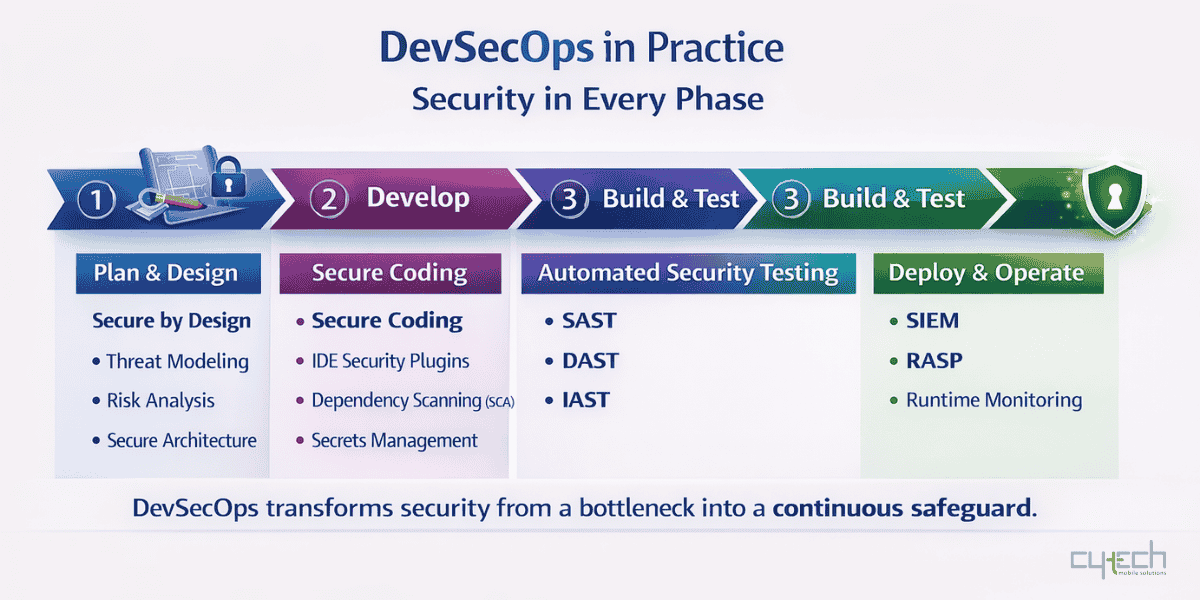
1. Plan & Design: Secure by Design
Security starts with the very first requirements. By performing Threat Modeling, teams can proactively identify potential attack vectors before a single line of code is written. This helps build countermeasures into the architecture rather than patching them in later.
2. Develop: Code-Level Security
Integrate security into the daily developer workflow using:
- IDE Plugins: Real-time alerts for insecure coding patterns.
- Software Composition Analysis (SCA): Automatically scanning open-source dependencies for known vulnerabilities (CVEs).
- Secrets Management: Ensuring API keys and credentials are never hardcoded in the source.
3. Build & Test: Automated Analysis
Incorporate security testing directly into the CI/CD pipeline:
- Static Application Security Testing (SAST): Analyzing source code for flaws without executing it.
- Dynamic Application Security Testing (DAST): Testing the running application from the outside in, mimicking an attacker’s perspective.
- Interactive Application Security Testing (IAST): Analyzing code execution in real-time during functional testing.
4. Operate: Continuous Monitoring
Security doesn’t end at deployment. Continuous monitoring using SIEM (Security Information and Event Management) and Runtime Application Self-Protection (RASP) ensures that any emerging threats or anomalies in the production environment are detected and mitigated instantly.
Overcoming Common Challenges
While the benefits are clear, implementing DevSecOps can present challenges such as cultural resistance or “tool fatigue.” Success depends on:
- Automation: Minimizing manual intervention to keep pace with rapid releases.
- Education: Empowering developers with security training so they feel capable, not hindered.
- Pragmatism: Starting small by automating the most critical checks first and expanding over time.
Conclusion: Security as an Enabler
Shifting left with DevSecOps is not just about adding security steps to the pipeline; it’s a fundamental change in mindset. By empowering teams and integrating automated tools, organizations transform security from a “blocker” into an accelerator. In a landscape where speed of delivery is critical, DevSecOps enables organizations to deliver high-quality, secure software faster and with greater confidence.

